How to Configure SCIM Provisioning using Okta
System for Cross-Domain Identity Management (SCIM) is an open standard protocol used to automate the exchange of user and group information between Identity providers and Enterprises. SCIM ensures that users added to the Identity Management System should have their accounts automatically created in VIDIZMO. User attributes and profiles are synchronized between the two systems, updating and removing users based on the user status or role change.
VIDIZMO offers a SCIM 2.0 REST API so that the pain of working with proprietary user management APIs or products can be reduced or eliminated. The knowledge of how to set up and test your application and API endpoints in order to be able to successfully deploy an OKTA integration using SCIM Provisioning is of utmost importance whether you are an independent software vendor (ISV), an existing OKTA user, or an IT systems administrator.
Prerequisites
- Ensure that you belong to a group where the Management of SSO + SCIM permission is enabled to access this feature.
- Before provisioning users and groups from Okta through SCIM protocol, make sure you have an OKTA IDP account so that you can configure the General Settings and any Sign-On Options for the VIDIZMO Application in OKTA.
Configuration Steps
VIDIZMO Configuration
Following are the steps to configure OKTA Provisioning in VIDIZMO:
In your VIDIZMO portal follow the steps to configure the Okta app.
-
Select the navigation menu on the top left corner.
-
Expand the Admin tab and select Portal Settings.
-
On the Portal Settings page, select the Apps tab.
-
Select Provisioning and locate the SCIM Okta App.
-
Select the Settings icon.
-
After selecting the Settings icon, a window will appear which offers various fields, each of which is explained below:
In order to enable the SCIM app first you need to perform the following actions:
i. Select a CAL.
NOTE:
- The default CAL is the CAL that will be assigned to the users by default during the time of provisioning from Okta if you have not explicitly defined any CAL.
- If multiple CAL (Client Access License) types are available in your VIDIZMO portal, you can select the desired CAL type. This selection will be automatically applied to all users who log in to the VIDIZMO portal using Okta SSO.
- If all available CALs have been consumed, any new user attempting to access SCIM functionality within the portal will receive a notification indicating that no CALs are available.
ii. Select Add New Rule if you want to configure the option of setting rules for automatic CAL assignment specifically for users belonging to specialized groups. Refer to How to Configure Rules for Automatic CAL Assignment using SCIM.
iii. Select Generate API Token to generate an API key against your domain for authorization purposes.
iv. Provide the expiry date to generate an API Key.
NOTE: The provisioning and de-provisioning management will be revoked from Okta once the expiry date limit exceeds.
v. Copy the generated API token to the clipboard and save the changes from the Save Changes button.
NOTE: This API Key will be used during the configuration of API Integration in Okta.
- Enable the app by selecting the toggle button.
NOTE: A notification will appear stating "Portal Information Updated Successfully."
OKTA Configuration
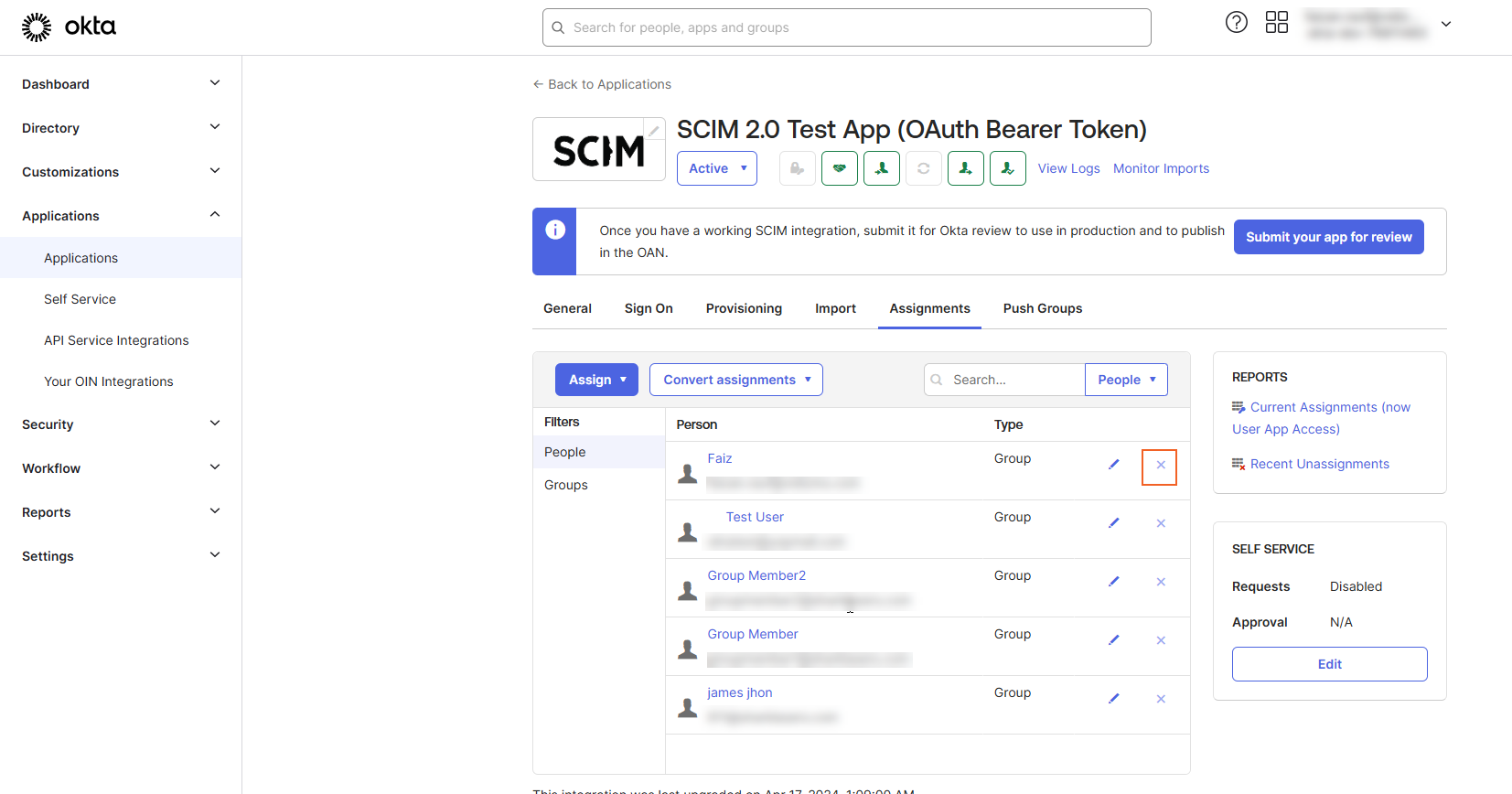
Following steps will be taken in the Okta account for building a connection with VIDIZMO portal in order to implement user provisioning in VIDIZMO. In Okta search for SCIM 2.0 Test App (OAuth Bearer Token) and complete the following configuration steps:
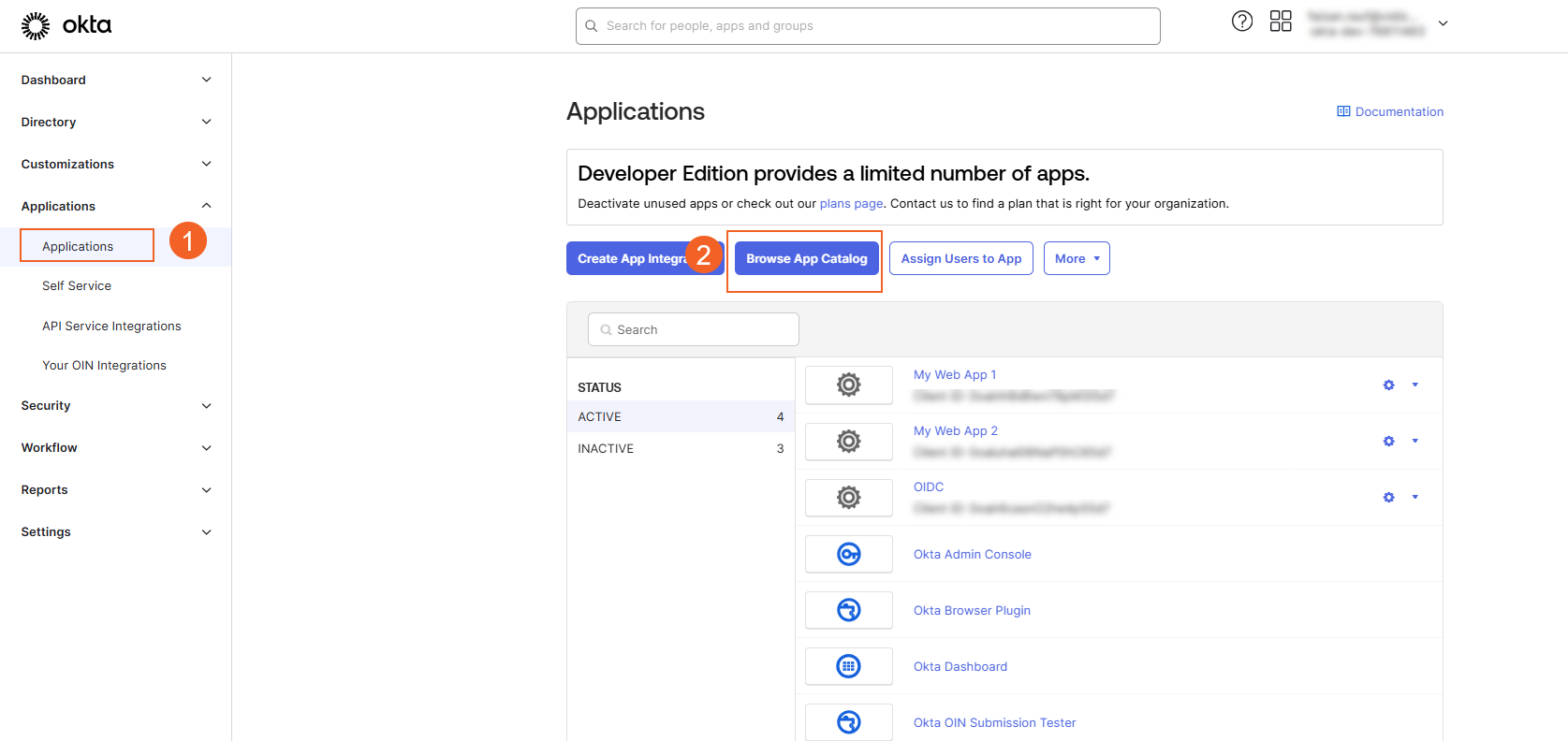
- Navigate to Applications in Okta Dashboard.
- Select the Browse App Catalog option.
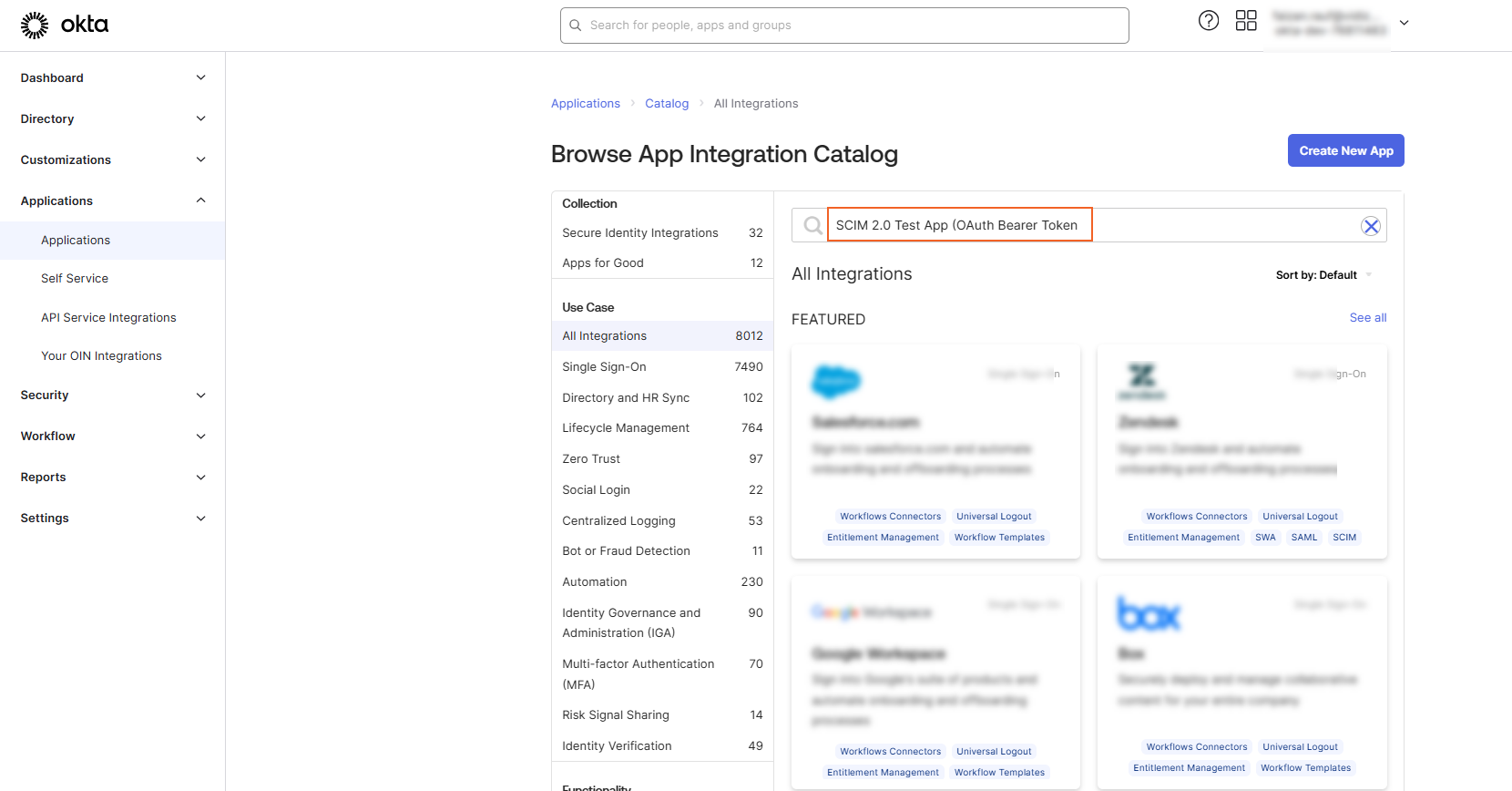
- Search SCIM 2.0 Test App (OAuth Bearer Token) and add it.
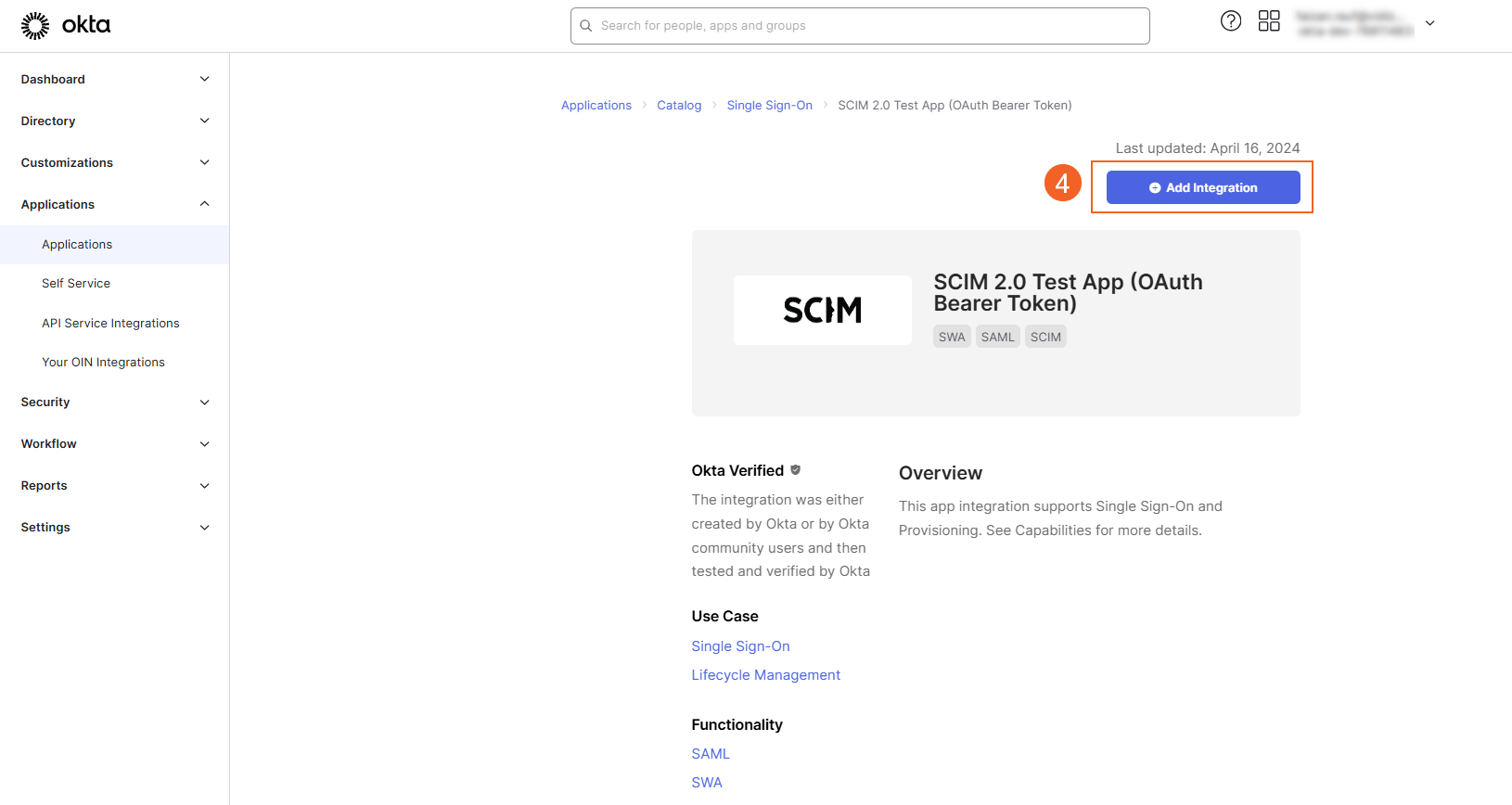
- Select Add Integration.
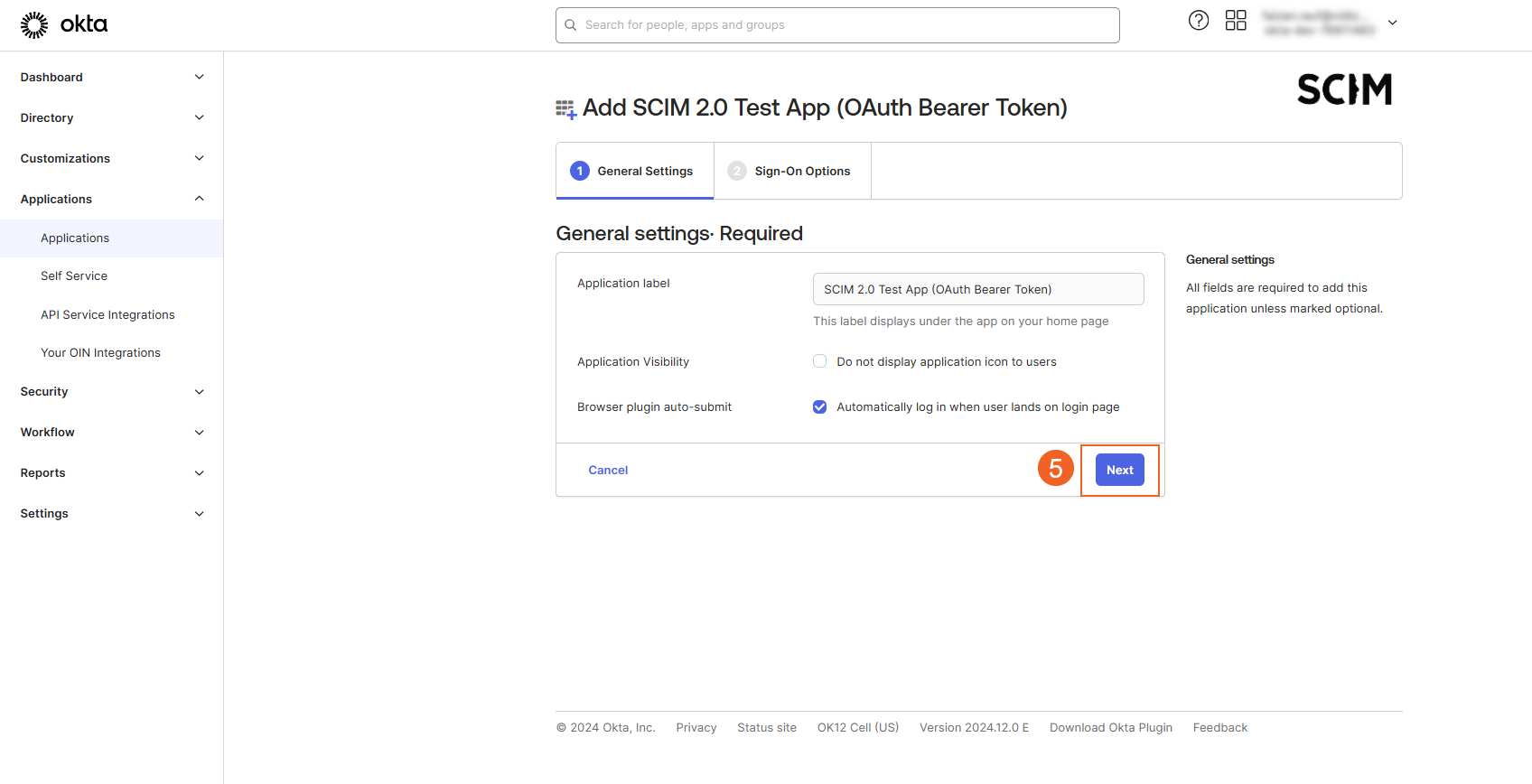
- Under the General Settings tab, select Next.
-
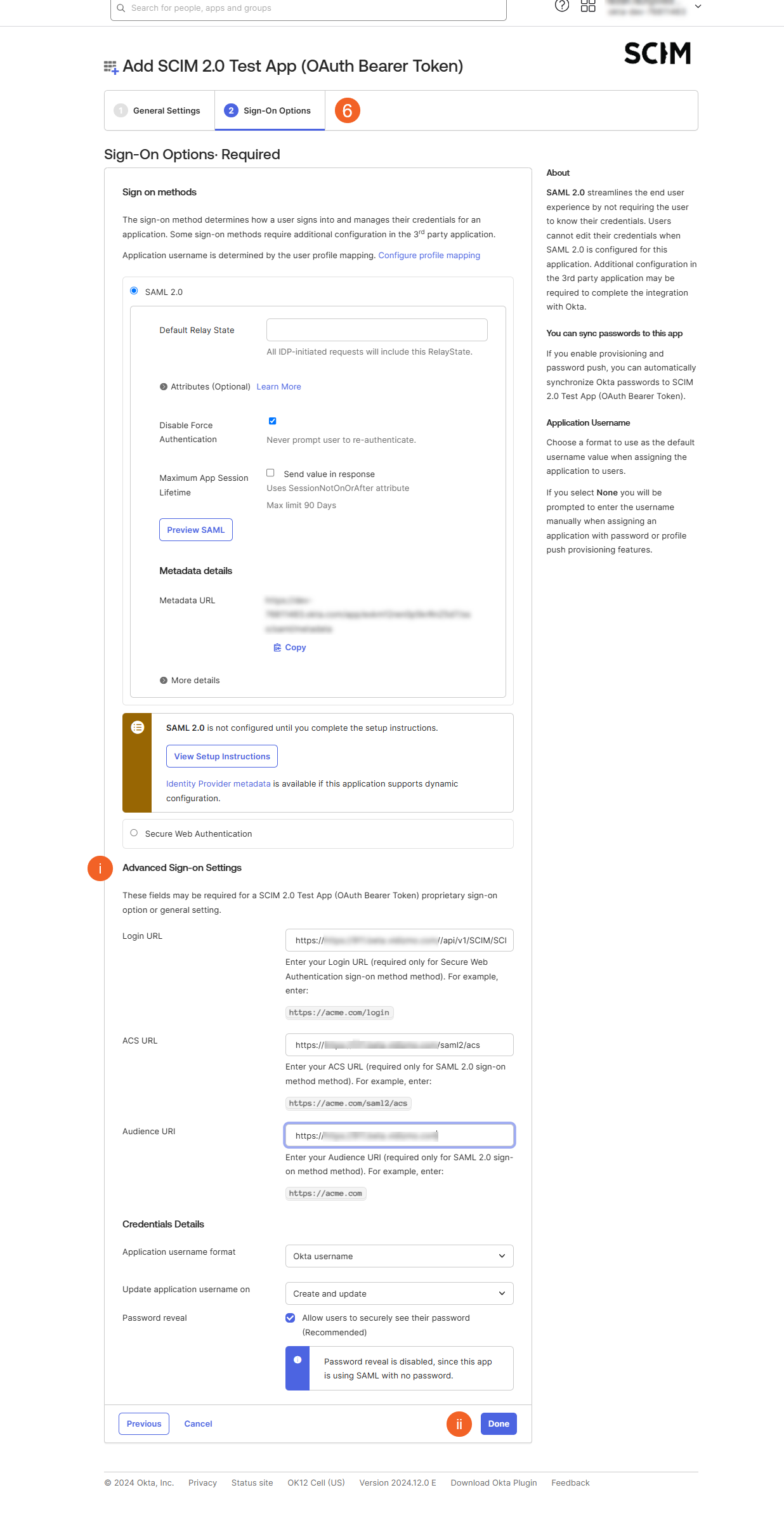
Navigate to the Sign-On Options tab.
i. Complete the following fields:
- Login URL: Enter the URL (for example,
https://your-portal/login). - ACS URI: Specify the ACS URI (for example,
https://your-portal/saml2/acs). - Audience URI: Provide the Audience URI (for example,
https://your-portal).
ii. Select Done to save the changes.
- Login URL: Enter the URL (for example,
-
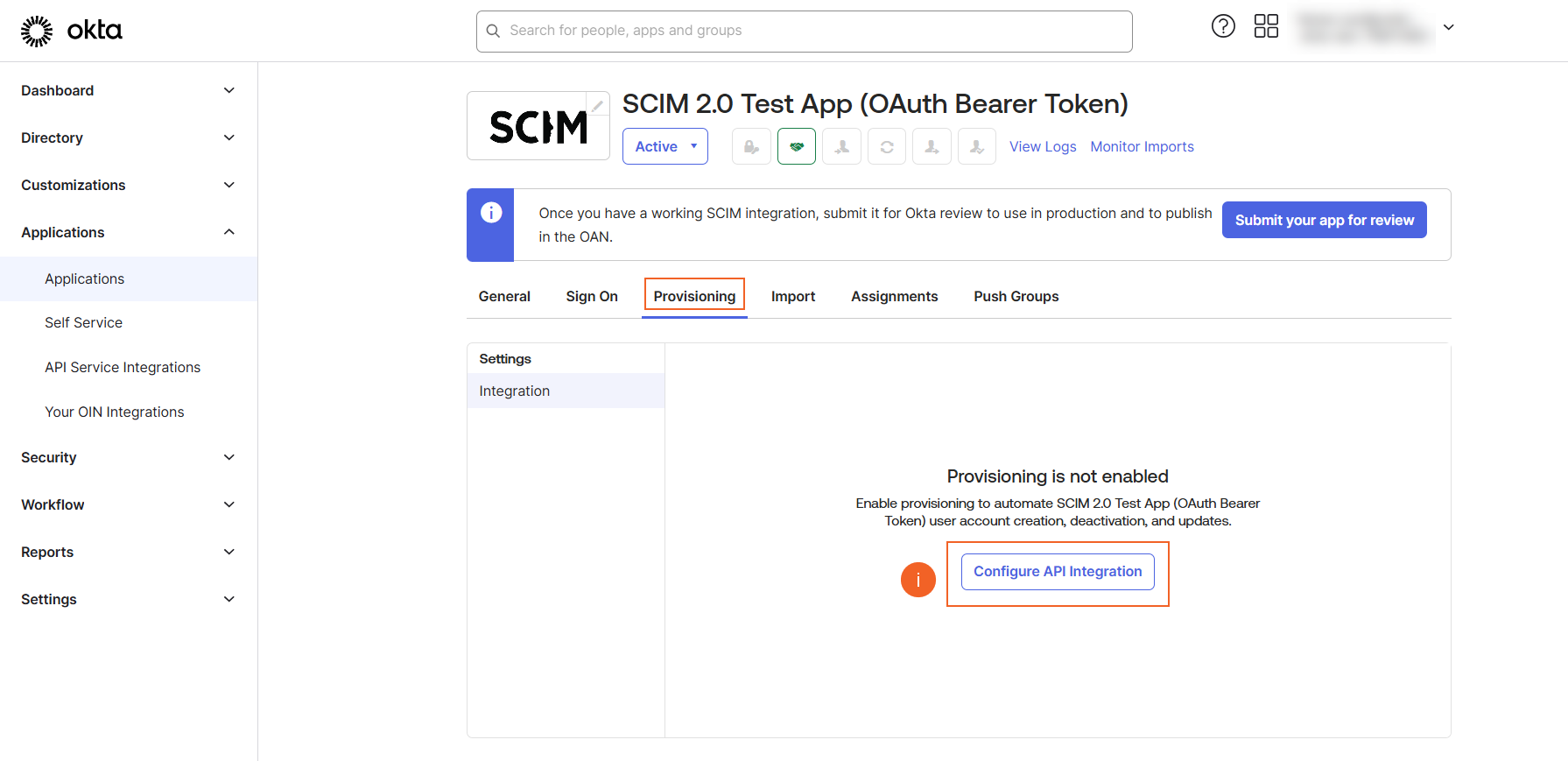
In the Provisioning tab:
i. Select Configure API Integration.
ii. Check the Enable API Integration option.
iii. For Base URI, follow the convention as https://YOUR-TENANT-SUBDOMAIN-HERE/api/v1/SCIM/SCIMOkta.
iv. For API Token, enter the value generated in the VIDIZMO portal.
v. Select the Test API Credentials button.
vi. Save the configuration if the configuration is successful.
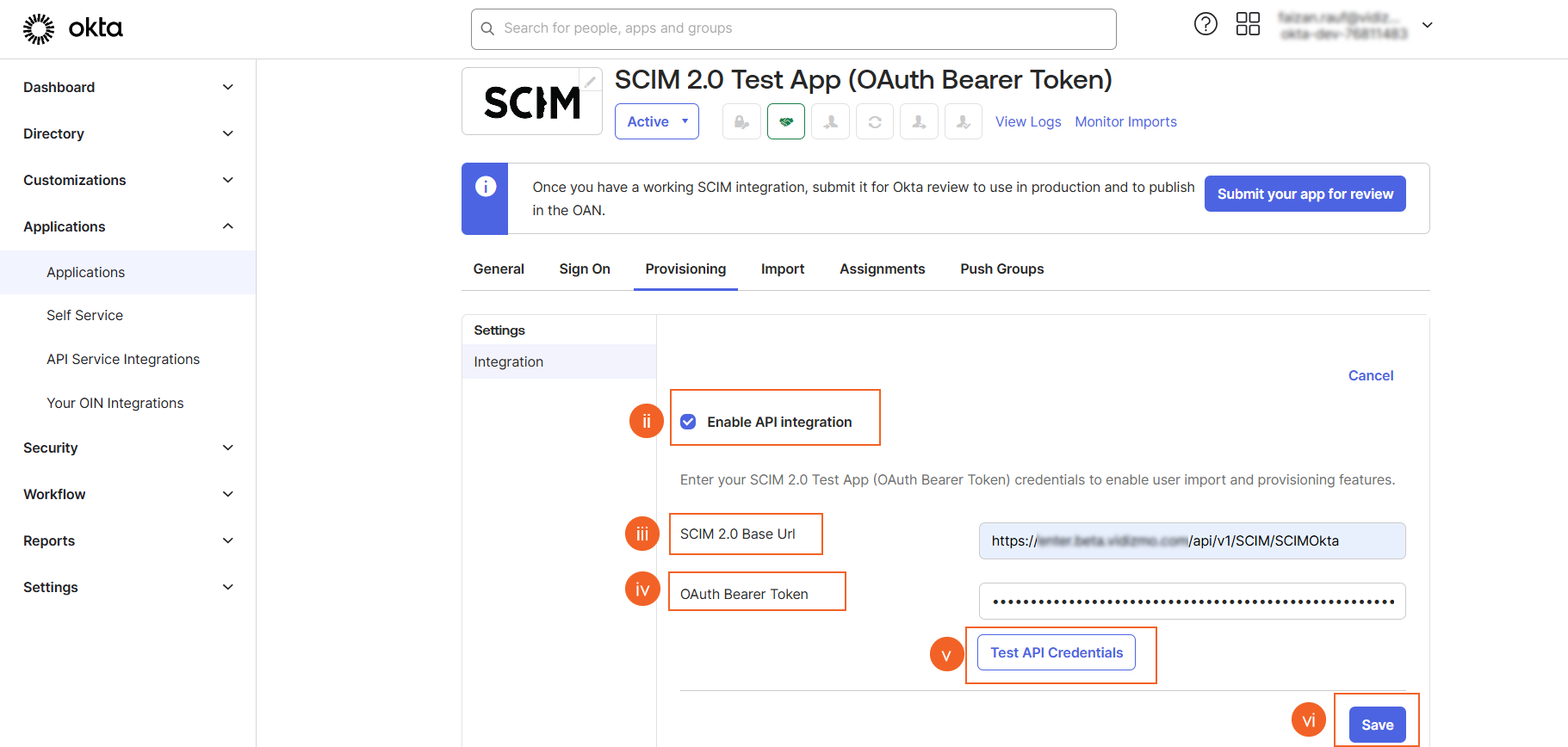
NOTE: The SCIM Provisioning is supported on portals created on sub-domains. To learn more about domain options in VIDIZMO, read more at Understanding Domain Options for a Portal.
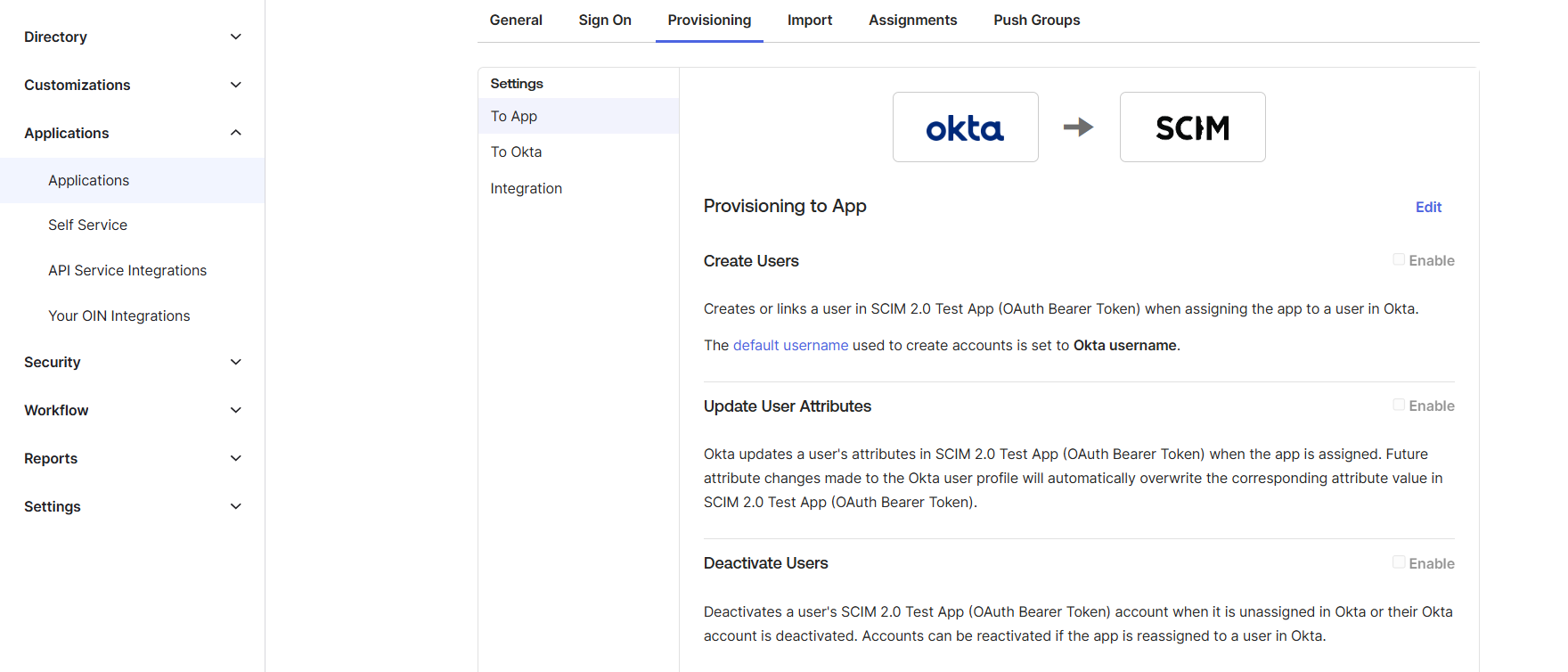
vii. Select the To App option in the left hand menu in the Provisioning tab and select the Provisioning Features that need to be enabled.
Provisioning
User(s)
Following are the steps to manage provisioning of users in Okta that are there in your directory folder to VIDIZMO portal.
Add Users
In order to add users in the VIDIZMO portal following steps needs to be followed:
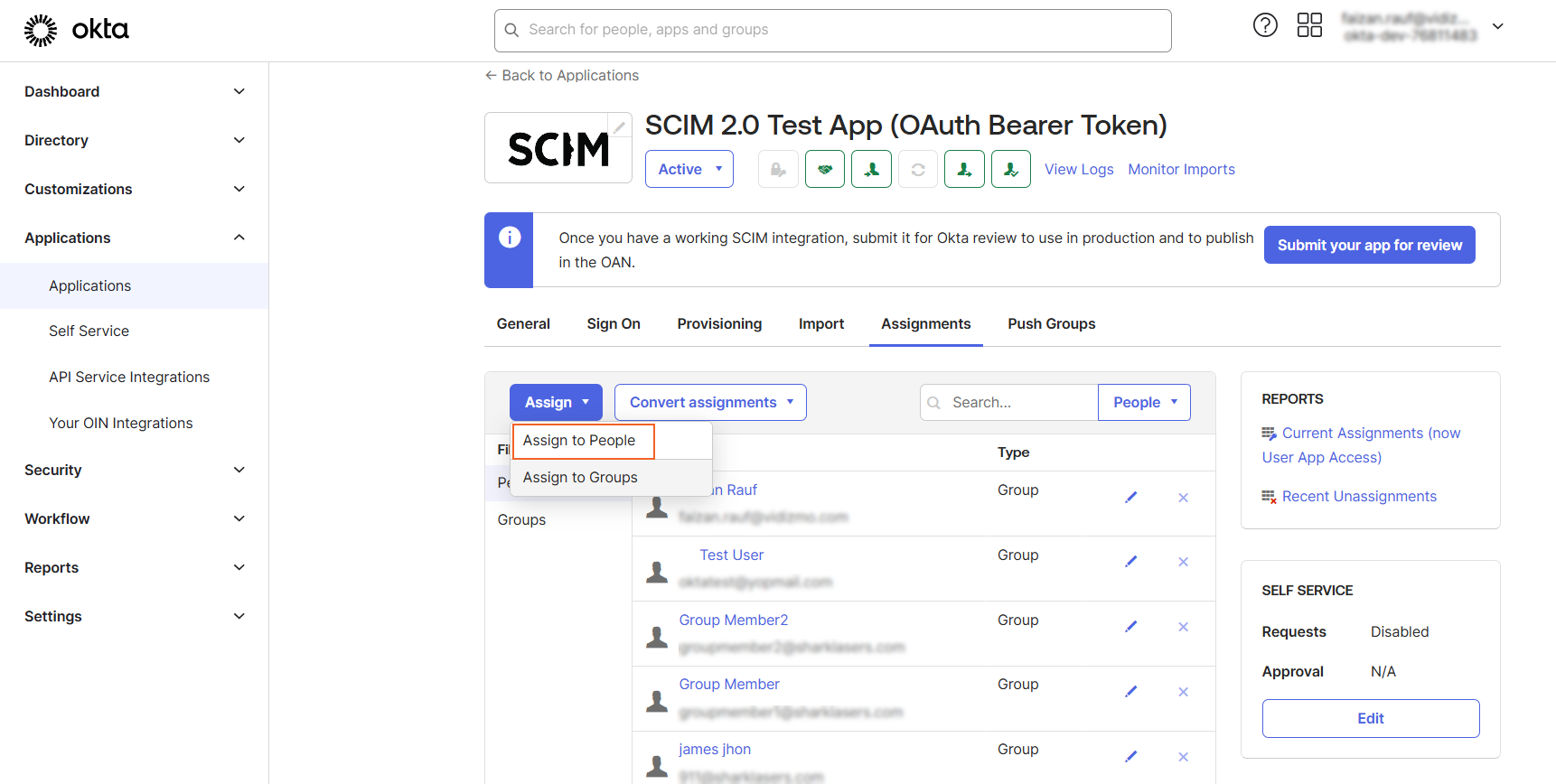
From the Assignments tab:
- Select the Assign option in order to start assigning users to the SCIM 2.0 App.
- Select the Assign to People option and choose users from the directory to assign them.
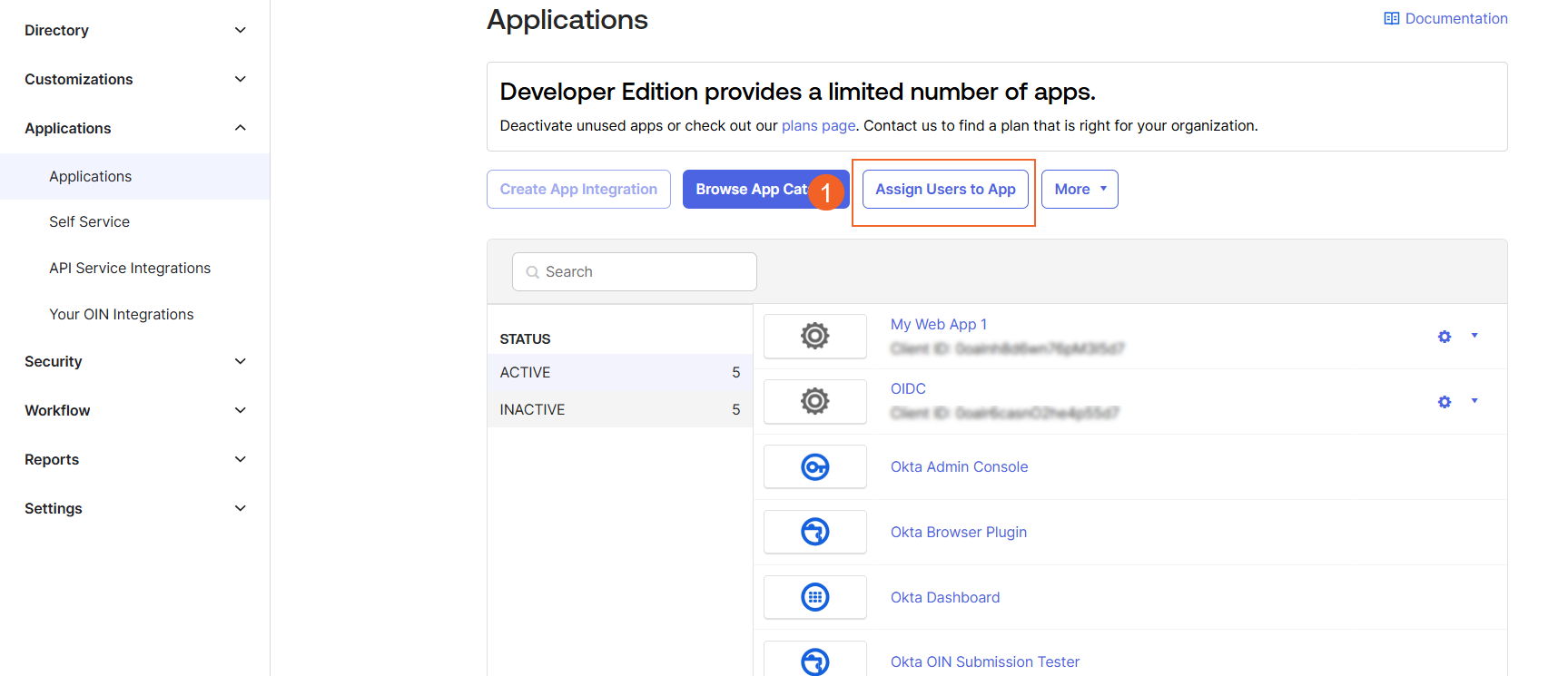
Bulk Add
Another way to assign users to application in Okta in bulk is as follows:
- In the Application tab, select Assign Users to App.
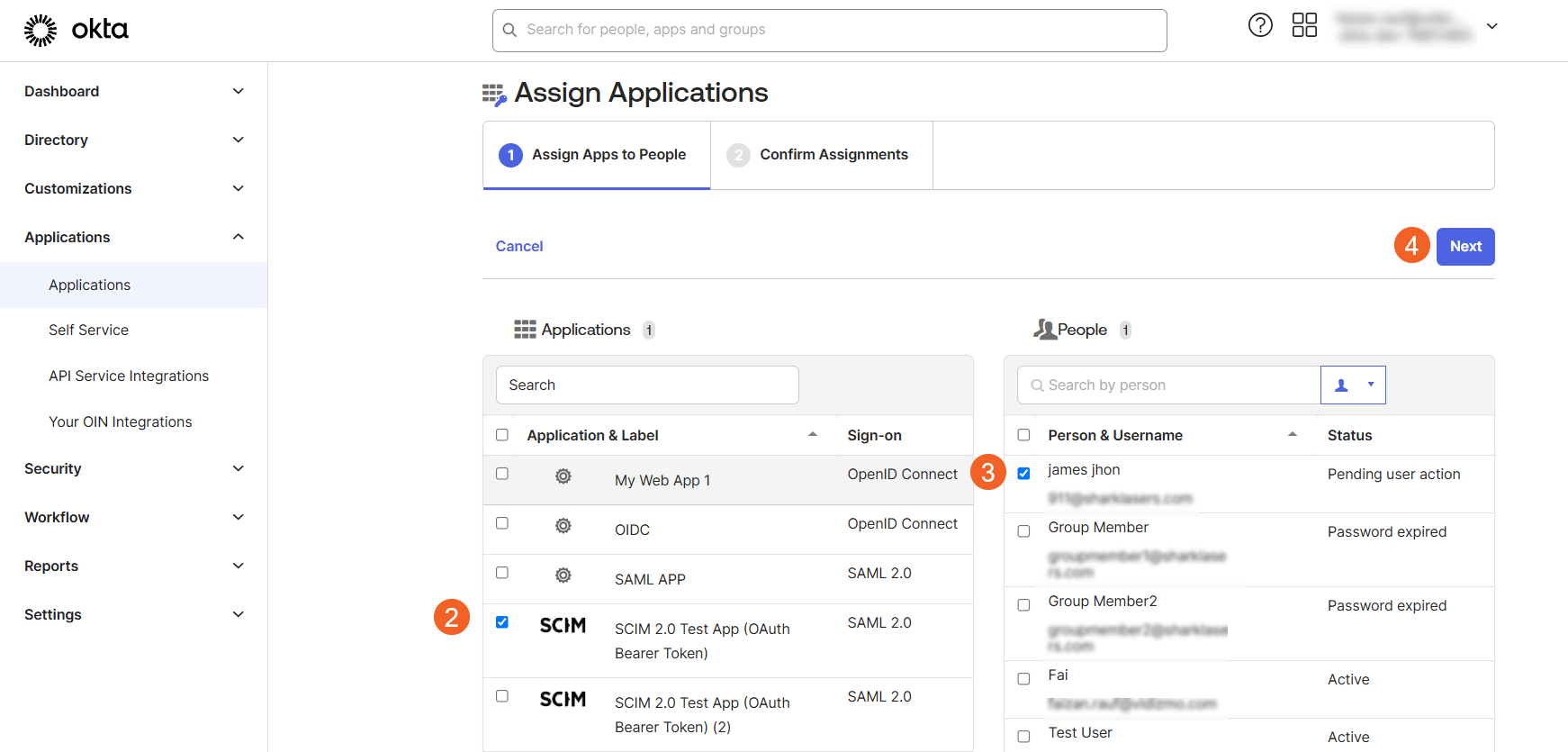
-
Select the users that you want to assign or simply check all the users that are present in your Okta directory.
-
Select the Application name from the applications tab that you want your users to be assigned in.
-
Select Next to confirm the assignments.
Edit
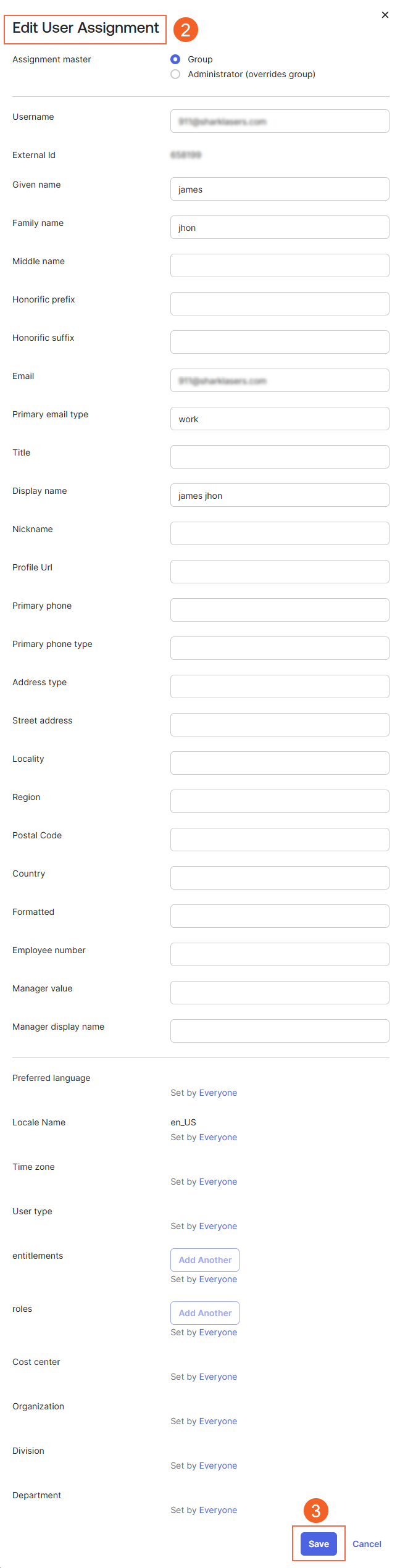
As SCIM provides a functionality of updating the user profile information as well, following steps should be followed to achieve this functionality:
- In the Assignments tab, on the name of the user you wish to update its profile information, select the edit button.
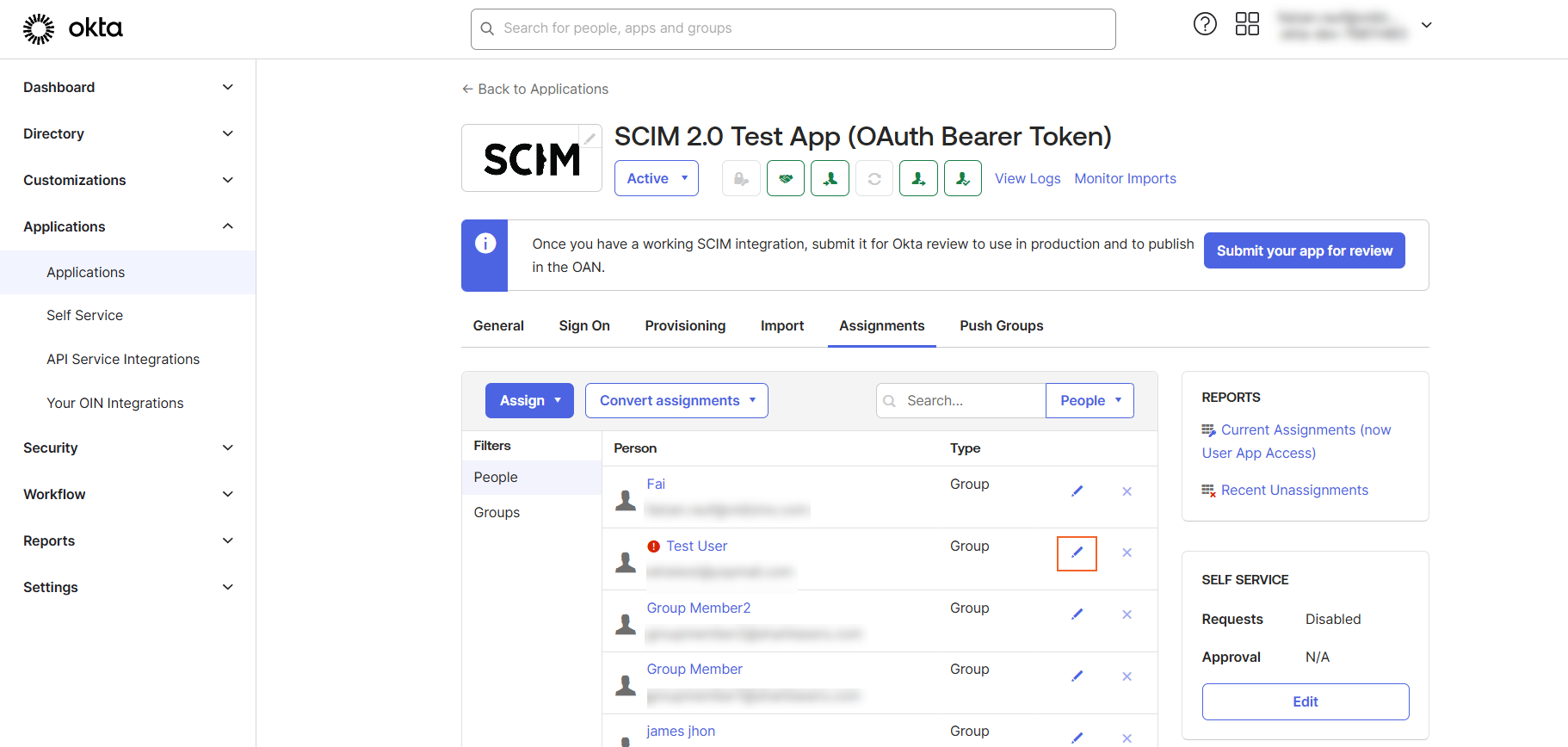
-
In the Edit User Assignment modal the profile information that can be edited is Email, First Name and Last Name.
-
Select Save.
Group(s)
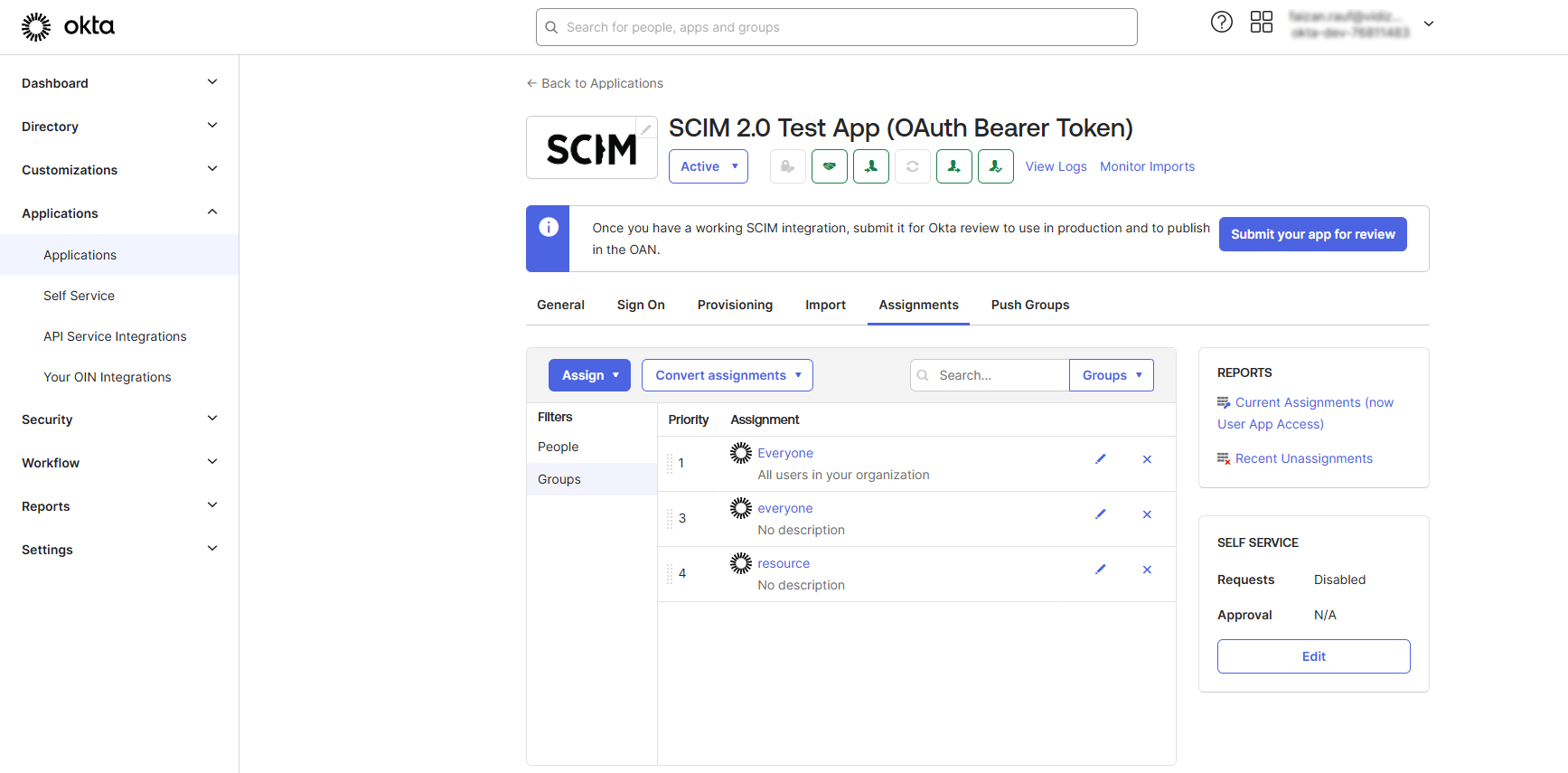
Following steps needs to be followed in order to provision groups in Okta to VIDIZMO Portal.
Add
In order to add groups in the VIDIZMO portal from Okta following steps needs to be followed:
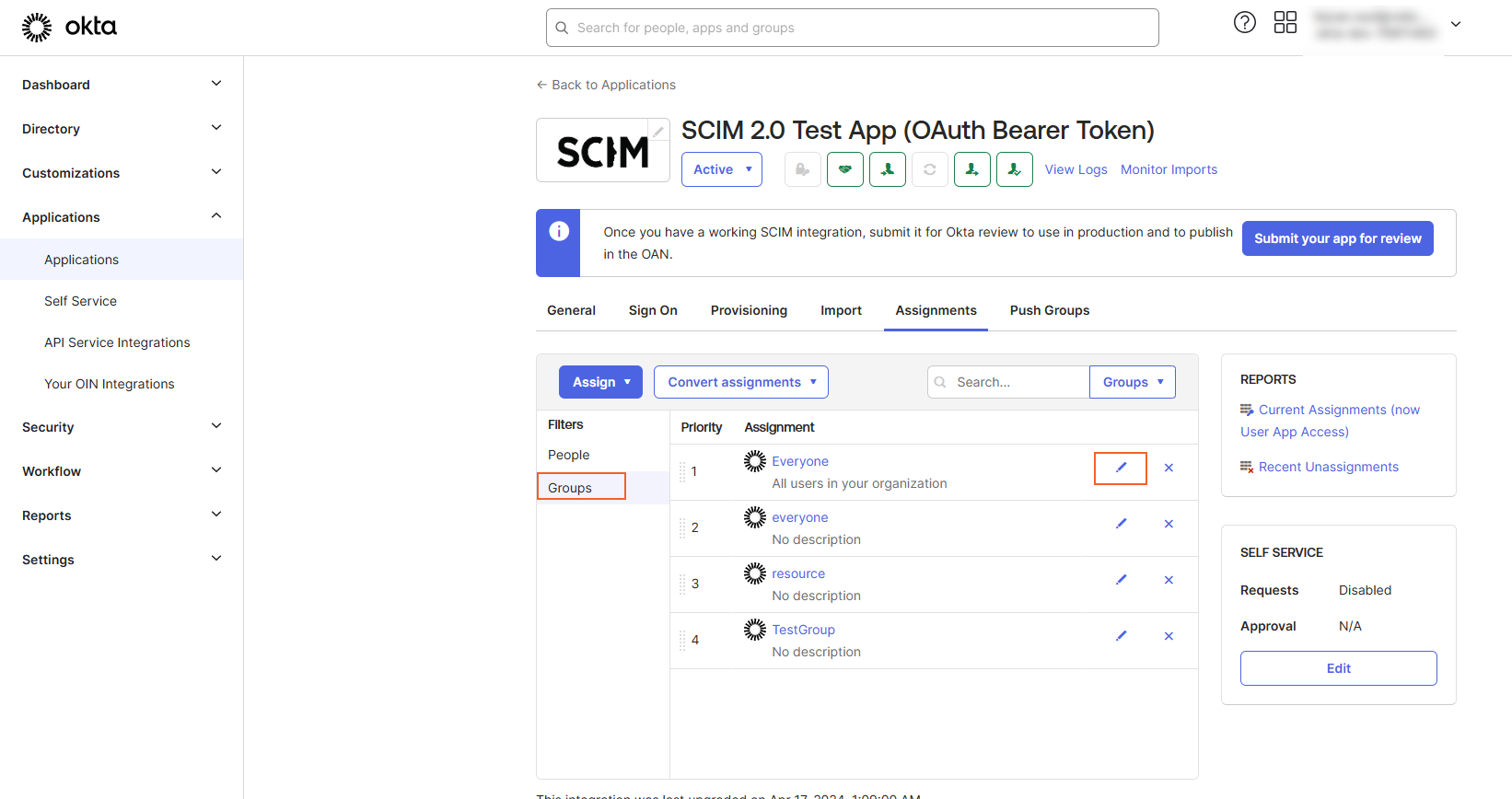
- Navigate to the Assignments tab. Select Assign to Groups option.
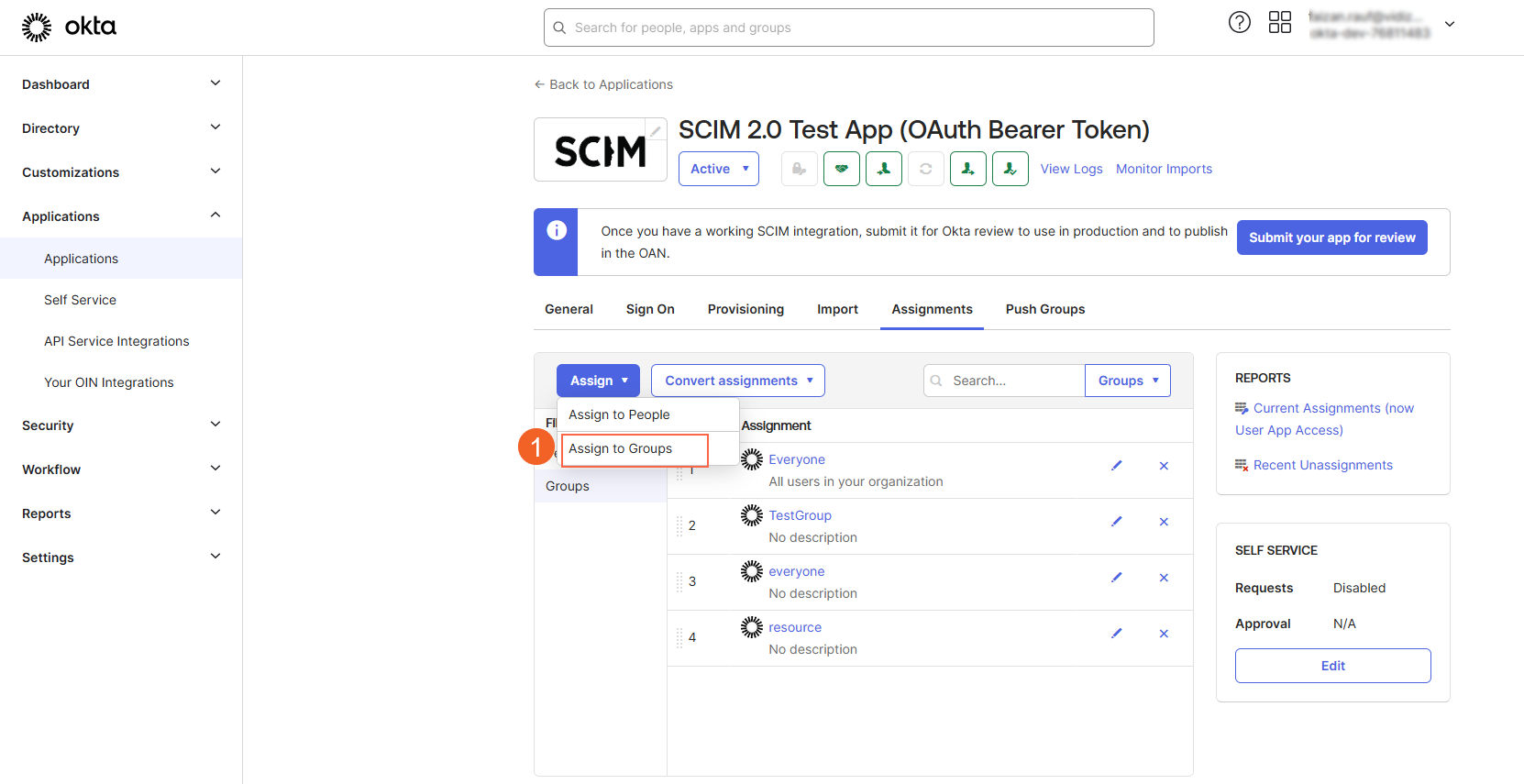
NOTE: Assign to groups is a very important step for all the users that are part of the pushed group to appear in the VIDIZMO Portal.
-
Search for the group that you need to assign to the SCIM 2.0 App. Select the Assign button.
-
Select the Save button.
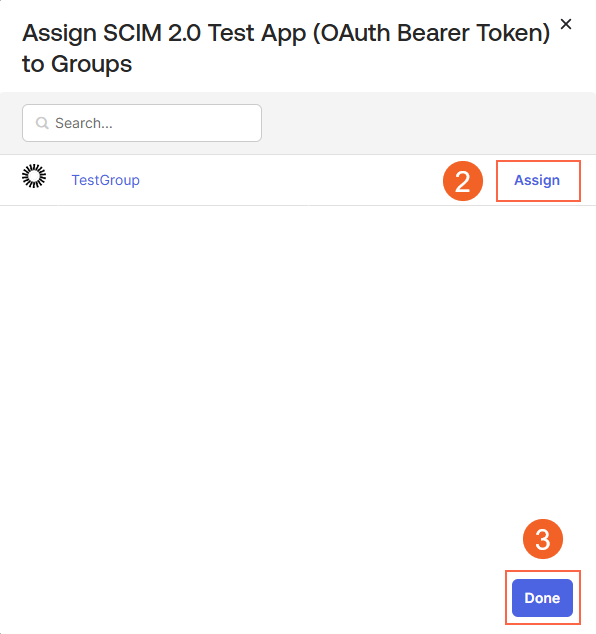
Assigned groups will be displayed in the list.
Push Groups
For pushing groups to VIDIZMO Portal:
- Navigate to the Push Groups tab in the SCIM App in OKTA.
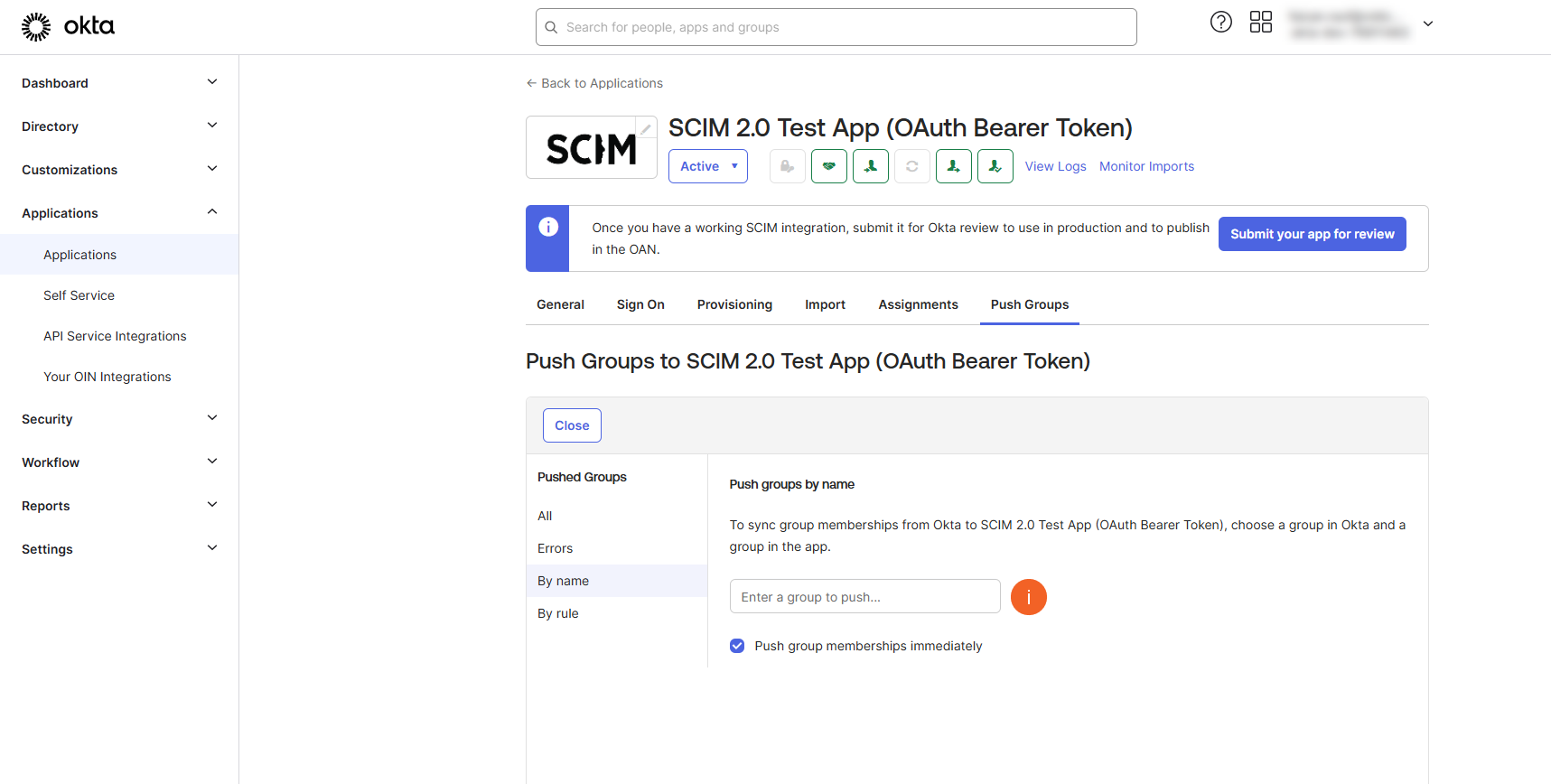
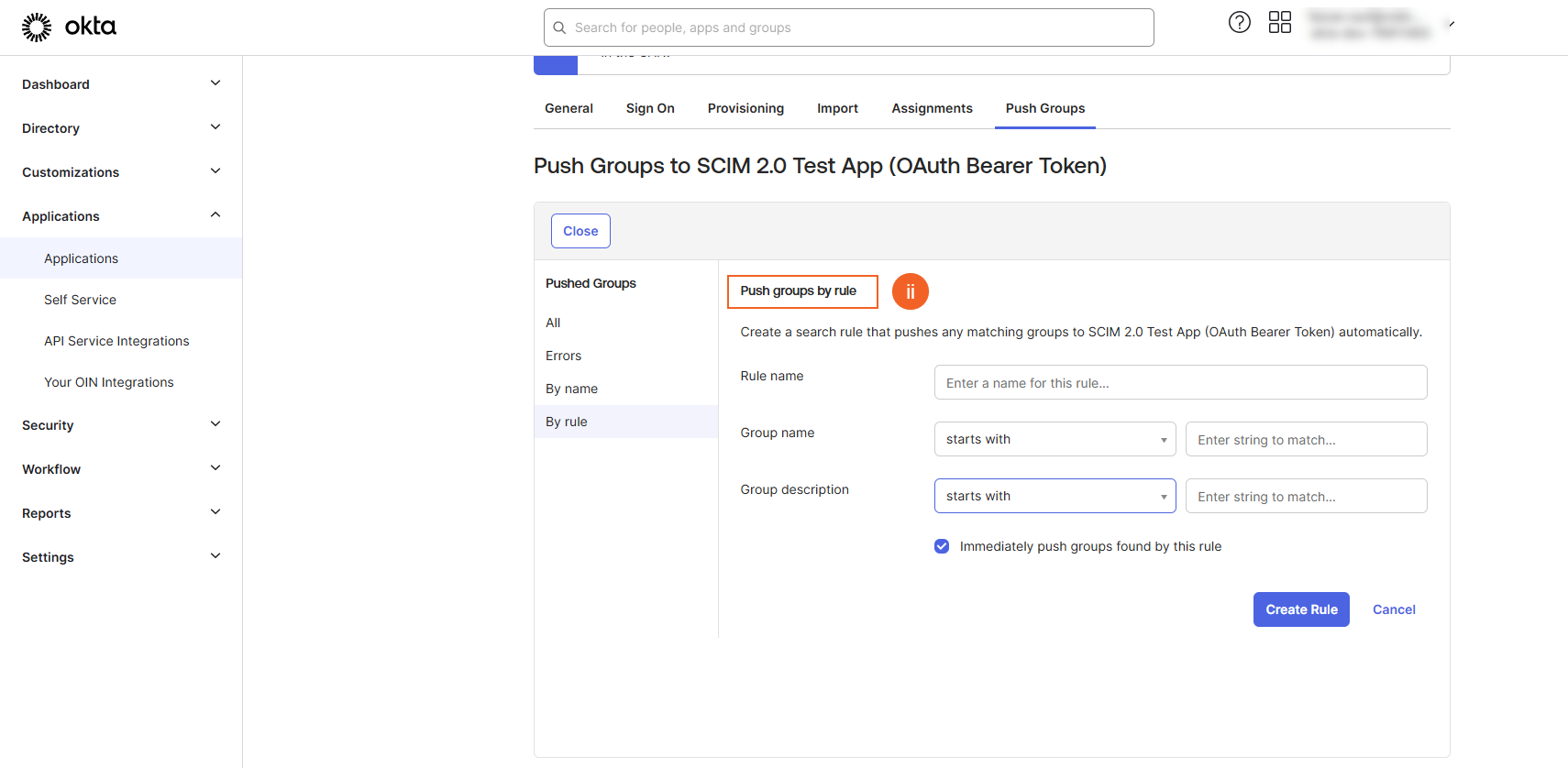
- Select Push Groups and choose the method for pushing the group to the VIDIZMO Portal.
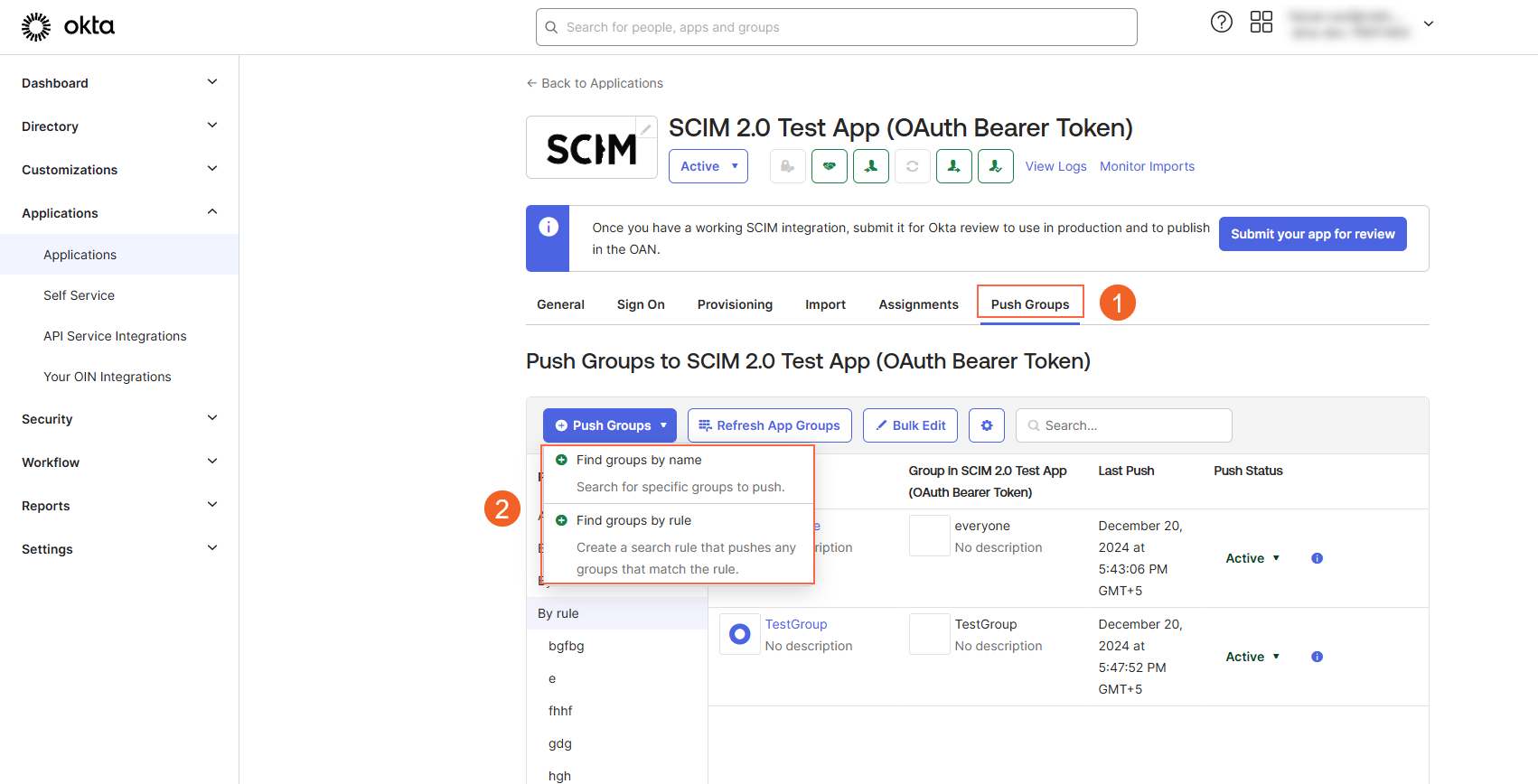
i. If you select Find groups by name, enter the name of a group to push.
OR
ii. If you select Push groups by rule, enter a name for the rule, group name and description and create rule.
- Now, you need to assign that pushed group in the Assignments tab.
Edit
The groups edit supported in VIDIZMO is the name of the group as of yet.
- To edit a group, navigate to the Assignments tab, select the Edit button next to the group, and make the necessary changes.
De-Provisioning
In order to deactivate the users or groups from the VIDIZMO Portal following steps should be followed:
- Navigate to the Users tab (or Groups tab for group-related actions).
- Locate the cross icon next to the user (or group) you wish to deactivate.
- Select the cross icon to initiate the deactivation.
- Confirm the deactivation by selecting OK.
Limitations
- Users cannot be permanently deleted from VIDIZMO, they will be deactivated instead. A deactivated user can be reactivated. When a user is deactivated via SCIM, VIDIZMO immediately disables their membership to their account, ensuring that their access is immediately revoked. The user is treated as an anonymous user in the VIDIZMO portal.
- Provisioned users cannot change their user profile information because they are treated as a Federated User in the VIDIZMO portal.
- Provisioning and deprovisioning can be enabled only on portals that are created under the subdomain policy. Learn more about domain options in VIDIZMO from Understanding Domain Options for a Portal.
Read Next
- How to Configure SCIM Provisioning using Azure AD
- How to Configure Rules for Automatic CAL Assignment using SCIM